A recent Bitvise SSH Client version should be used on all platforms. The SSH Client is security-sensitive software that communicates across a network. Using a recent version is the only way to receive updates. Therefore, we do not recommend indefinite use of older versions. Encryption and security features. SSH and SFTP: Key exchange algorithms.
- Sftp - ssh SFTP (SSH File Transfer Protocol) is a network protocol that provides file access, file transfer, and file management over any reliable data stream. It was designed by the Internet Engineering Task Force (IETF) as an extension of the Secure Shell protocol (SSH) version 2.0 to provide secure file transfer capabilities.
- Sftp - ssh SFTP (SSH File Transfer Protocol) is a network protocol that provides file access, file transfer, and file management over any reliable data stream. It was designed by the Internet Engineering Task Force (IETF) as an extension of the Secure Shell protocol (SSH) version 2.0 to.
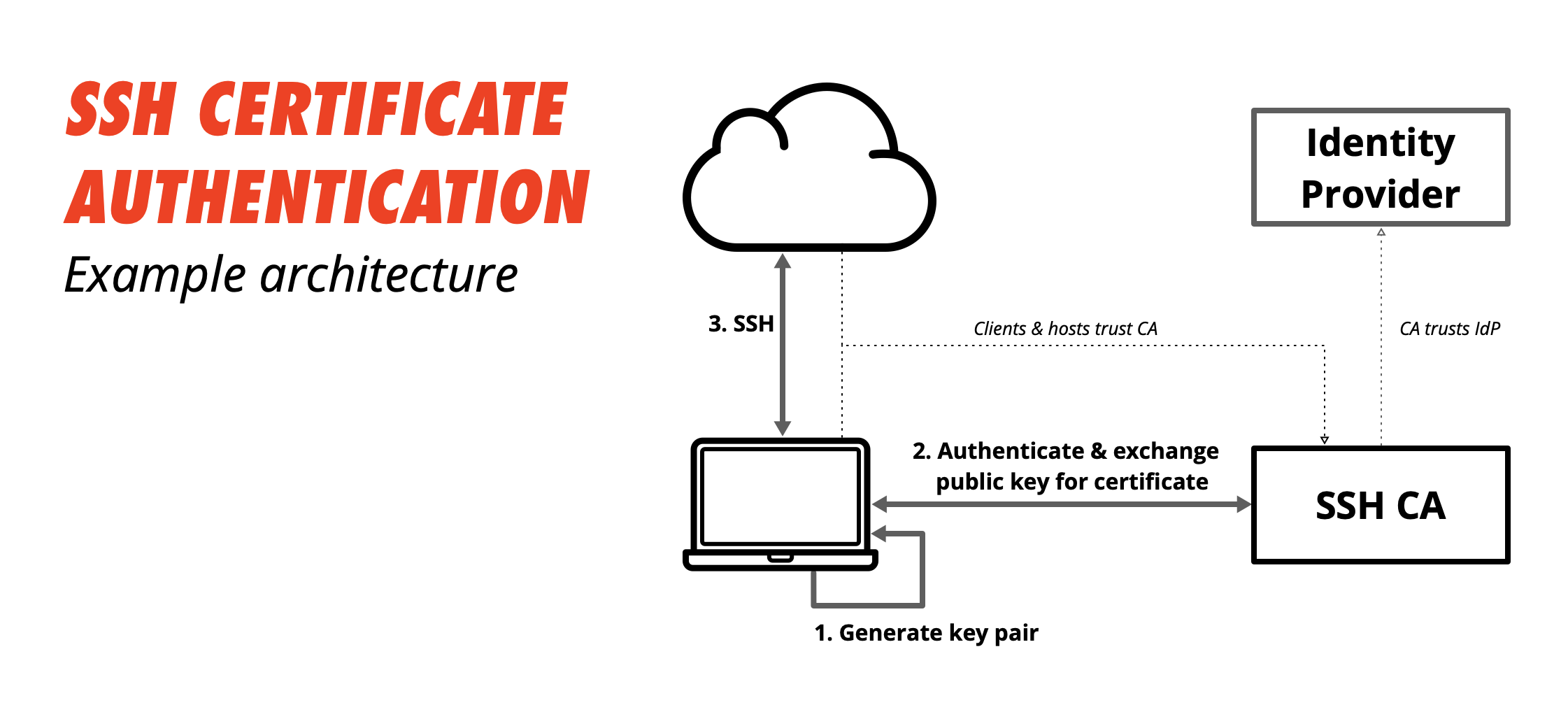
- SSH public key authentication remains an option for researchers who submit the 'SSH public key authentication to HPS systems' agreement (log into HPC everywhere using your IU username and passphrase), in which you agree to set a passphrase on your private key when you generate your key pair.
- The term SFTP can also refer to Secure file transfer program, a command-line program that implements the client part of this protocol. As an example, the sftp program supplied with OpenSSH implements this. Some implementations of the scp program support both the SFTP and SCP protocols to perform file transfers, depending on what the server.
Our SSH client supports all desktop and server versions of Windows, 32-bit and 64-bit, from Windows XP SP3 and Windows Server 2003, up to the most recent – Windows 10 and Windows Server 2019.
Our client is free for use of all types, including in organizations. To begin, simply download it here.
Our SSH and SFTP client for Windows incorporates:
One of the most advanced graphical SFTP clients.
Single-click Remote Desktop forwarding.
State-of-the-art terminal emulation with support for the bvterm, xterm, and vt100 protocols.
Support for corporation-wide single sign-on using SSPI (GSSAPI) Kerberos 5 and NTLM user authentication, as well as Kerberos 5 host authentication.
Support for ECDSA, RSA and DSA public key authentication with comprehensive user keypair management.
Encryption and security: Provides state-of-the-art encryption and security suitable as part of a standards-compliant solution meeting the requirements of PCI, HIPAA, or FIPS 140-2 validation.
Obfuscated SSH with an optional keyword. When supported and enabled in both the client and server, obfuscation makes it more difficult for an observer to detect that the protocol being used is SSH. (Protocol; OpenSSH patches)
Powerful SSH port forwarding capabilities, including dynamic forwarding through integrated SOCKS and HTTP CONNECT proxy.
Powerful command-line parameters which make the SSH client highly customizable and suitable for use in specific situations and controlled environments.
An FTP-to-SFTP bridge allowing you to connect to an SFTP server using legacy FTP applications.
An advanced, scriptable command-line SFTP client, sftpc.
A scriptable command-line remote execution client, sexec, and a command-line terminal console client, stermc.
A scriptable command-line tunneling client, stnlc, with support for static port forwarding rules, dynamic SOCKS-based tunneling, and FTP-to-SFTP bridge.
Our .NET SSH library, FlowSshNet, with example PowerShell scripts showing how to use the SSH library for file transfer and remote program execution from PowerShell.
Bitvise SSH Server remote administration features.
Bitvise software does not contain ads, install product bundles or collect user data for sale. We are 100% supported by users who license our software. Thank you!
Bitvise SSH Client incorporates one of the most advanced SFTP file transfer clients, supporting:
- automatic resuming, text file awareness, recursive subdirectory transfers;
- powerful, advanced transfer list management;
- verified-integrity resume with servers that support SFTP v6 check-file and check-file-blocks;
- directory mirroring with servers that support SFTP v6 check-file and check-file-blocks;
- high speed - in tens or hundreds of MB/s with Bitvise SSH Server, network and disk speed permitting;
- fast responsiveness to user input even when in the middle of multiple file transfers.
Bitvise SSH Client also incorporates an advanced, scriptable command-line SFTP client.
Bitvise SSH Client provides integrated access to the SSH server's console, either via VT-100 and xterm protocols supported by most SSH servers on any platform, or via the enhanced bvterm protocol supported by Bitvise SSH Server:
- all terminal emulation is done in a regular Windows console, using standard Windows fonts, supporting standard settings for Windows consoles;
- UTF support with VT-100 and xterm, Unicode support with bvterm (full Unicode support on NT-series Windows platforms);
- full color support with xterm and bvterm;
- support for large screen buffers, all key combinations including Alt-keys and accurate console rendering with bvterm (fully accurate on NT-series Windows platforms).
Bitvise SSH Client also incorporates a command line terminal emulation client, stermc, as well as a command-line remote execution client (sexec).
When using Bitvise SSH Client to connect to a GSSAPI-enabled SSH server in the same or a trusted Windows domain, you can let Kerberos 5 (or on older platforms, NTLM) perform the server as well as user authentication for you. No manual host key verification; no management of user passwords and public keys. Just tell the SSH client which server in the domain to connect to, and if that server is Bitvise SSH Server (WinSSHD) or another server with compatible support for GSSAPI, the two programs will authenticate and establish a secure connection automatically.
Bitvise SSH Client is a powerful SSH2 port forwarding client with many features, including:
Dynamic tunneling via integrated proxy supporting SOCKS4, SOCKS4A, SOCKS5 and HTTP CONNECT proxy tunneling protocols. Configure your applications to connect to target hosts through the SSH Client's proxy, and no manual tunneling rules need be configured.
How to set up programs for dynamic tunneling: Firefox, IE; with these settings in Bitvise SSH Client.
Port forwarding settings can be saved to and loaded from a profile. One can maintain multiple complex tunneling configurations without having to manually enter parameters before each session.
Bitvise SSH Client minimizes its presence by displaying only a system tray icon when running in the background. If an error is encountered while the program is minimized, the icon reflects that.
Server-side forwarding: with Bitvise SSH Server and Client, a server and multiple clients can be set up so that all port forwarding rules are configured centrally at the server, without requiring any client-side setting updates. The SSH clients only need to be configured once, and port forwarding rules can easily be changed when necessary.
Command-line parameters are supported. Using command-line automation, a port forwarding session can be started from a link in the Startup menu without requiring any user interaction whatsoever. Help with the command-line parameters can be found in the SSH client log area when it is first started, or by executing 'BvSsh /?' from a command prompt.
After an SSH session is established, any external application can be launched automatically.
If an SSH session is interrupted, Bitvise SSH Client can automatically reconnect to the server.

Bitvise SSH Client also incorporates an advanced, scriptable command-line tunneling client.
Run 'BvSsh -?' for a list of command-line parameters providing flexibility to:
make Bitvise SSH Client load a profile and connect immediately on startup and exit on disconnect using the -profile, -loginOnStartup and -exitOnLogout parameters;
make Bitvise SSH Client hide portions of its user interface (main window, authentication messages, access to SSH features) using the -hide and -menu parameters;
run Bitvise SSH Client from removable media and prevent it from making any changes to the Windows registry - and yet use public key authentication and verify host keys using the -noRegistry, -keypairFile and -hostKeyFile parameters;
and more.
Additionally, when the graphical Bitvise SSH Client is running, you can use the command line utility BvSshCtrl to programmatically cause the client to log in, log out, or exit. Run 'BvSshCtrl' for help.
Bitvise SSH Client (Tunnelier) supports command-line parameters that control how it uses the Windows registry (the -noRegistry and -baseRegistry parameters). This can be used when control over registry usage is required.
The latest versions of our SSH Client additionally support storing host key information and client authentication keypairs in an SSH Client profile. This means that you can copy the contents of the SSH Client installation directory to a USB key, insert the USB key into another computer, and run the graphical SSH Client as follows:
BvSsh -noRegistry -profile=U:Profile.bscp
This will tell the Client to not use the Windows registry, and to connect exclusively using the host and keypair information you have saved into Profile.bscp.
For more information about the supported command line parameters, run the graphical SSH Client as follows:
BvSsh -?
Bitvise SSH Client further includes command line clients – sftpc, sexec, stermc, and stnlc – which also support the -noRegistry and -profile parameters. These command line clients are frequently used unattended, but can also be used interactively. For more information, check Using Bitvise SSH Client Unattended.
Bitvise SSH Client incorporates sftpc, an advanced command-line SFTP client which supports:
- queued background transfers so you can continue browsing directories while a file downloads ('get * -bg');
- powerful command-line parameters for automated scripted transfers launched from a batch file or an external program;
- verified-integrity resume with servers that support SFTP v6 check-file and check-file-blocks;
- automatic text file conversion when transferring files between platforms (the 'type' command);
- wildcards - the * and ? wildcard characters can match more than one file;
- recursive transfers - a simple 'get * -s' downloads all files and subdirectories;
- resume support - 'get file.txt -r' resumes a previously downloaded file if it already exists;
- high speed - in the tens of MB/s with Bitvise SSH Server, network and disk speed permitting.
Additional information:
Usage: after installing Bitvise SSH Client, get this help by executing 'sftpc -?'
Command list: after installing Bitvise SSH Client, get this help by connecting to a server using sftpc, then execute 'help' and 'help <command>'
The 'log' utility can be used with sftpc to store the output of each individual SFTP session in a separate, uniquely named log file for auditing.
The 'retry' utility can be used with sftpc to automatically repeat transfer attempts after specific types of failures.
Bitvise SSH Client incorporates sexec, a scriptable command-line remote execution client which can be used to securely execute programs on remote machines from a batch file. The batch file can perform actions based on the exit code reported from the remote program, and can capture the remote program's output for processing by simple redirection of sexec output.
Another command-line program included with Bitvise SSH Client, stermc, conveniently opens an SSH terminal emulation session with xterm, VT-100 and bvterm support in the same Command Prompt window it is started from. If you SSH from computer A to computer B running Bitvise SSH Server, and you also have Bitvise SSH Client installed on computer B, you can use stermc to conveniently establish an onward SSH terminal session to computer C.
All Bitvise command-line clients support all authentication methods supported by Bitvise SSH Client, can load settings from a profile configured in the graphical client, work with the same user keypair and host key database as the graphical client, can connect through a SOCKS or HTTP CONNECT proxy, and support a common set of command-line parameters controlling most aspects of establishing an SSH connection.
Bitvise SSH Client incorporates stnlc, a scriptable command line port forwarding client with support for static port forwarding rules, dynamic SOCKS-based tunneling, as well as the FTP-to-SFTP bridge.
Create Ssh Key For Sftp User
For more information about using this client, run 'stnlc -h'.
Bitvise SSH Client incorporates an FTP-to-SFTP bridge which performs translation between the FTP and SFTP protocols, allowing any FTP client application to connect securely to an SFTP server through Bitvise SSH Client. Both active mode and passive mode FTP data connections are supported, as well as restarted transfers, directory listings and other features. All FTP clients should be able to list directories and transfer files across Bitvise SSH Client's FTP-to-SFTP bridge, including integrated clients in applications such as DreamWeaver, GUI clients such as BulletProof FTP, and command line clients such as the default ftp.exe client accompanying Windows. If an FTP client you use fails to work with Bitvise SSH Client's FTP-to-SFTP bridge, let us know.
See Accessing an SFTP Server with an FTP Client for more information about the FTP bridge.
When connected to Bitvise SSH Server, our client can do all of the above, as well as the following:
bvterm console: When connected to Bitvise SSH Server, our client provides you with the best console available on the Windows platform. Our bvterm protocol supports the full spectrum of a Windows console's features: colors, Unicode characters, all-key access and large scrollable buffers.
Remote server configuration: Using Bitvise SSH Client, all SSH Server settings can be configured remotely without having to use Remote Desktop.
Bitvise SSH Client supports the following Windows versions:
- Windows Server 2019
- Windows Server 2016
- Windows 10
- Windows Server 2012 R2
- Windows Server 2012
- Windows 8.1
- Windows Server 2008 R2
- Windows Server 2008
- Windows Vista SP1 or SP2
- Windows Server 2003 R2
- Windows Server 2003
- Windows XP SP3
A recent Bitvise SSH Client version should be used on all platforms. The SSH Client is security-sensitive software that communicates across a network. Using a recent version is the only way to receive updates. Therefore, we do not recommend indefinite use of older versions.
Setup Ssh Key For Sftp
SSH and SFTP:
Key exchange algorithms:
- Curve25519
- ECDH over elliptic curves secp256k1, nistp256, nistp384, nistp521 using SHA-512, SHA-384, or SHA-256
- Diffie Hellman with group exchange using SHA-256 or SHA-1
- Diffie Hellman with fixed 4096, 3072, 2048, or 1024-bit group parameters using SHA-512, SHA-256, or SHA-1
- GSSAPI key exchange using Diffie Hellman and Kerberos authentication
Signature algorithms:
- Ed25519
- ECDSA over elliptic curves secp256k1, nistp256, nistp384, nistp521 using SHA-512, SHA-384, or SHA-256
- RSA using 4096, 3072, 2048, 1024-bit key sizes with SHA-512, SHA-256, or SHA-1
- DSA using SHA-1 (legacy)
Encryption algorithms:
- AES with 256, 128-bit keys in GCM mode
- AES with 256, 192, 128-bit keys in CTR mode
- AES with 256, 192, 128-bit keys in CBC mode (legacy)
- 3DES in CTR or CBC mode (legacy)
Data integrity protection:
- AES with 256, 128-bit keys in GCM mode
- HMAC using SHA-256, SHA-1
Server authentication:
- Client verifies server identity using server host key fingerprint or public key
- Automatic synchronization of new host keys to client supported
Client authentication:
- Password authentication with Windows accounts - local or Active Directory
- Password authentication with virtual accounts - configurable password policy
- Public key authentication
- Kerberos single sign-on using GSSAPI
- Two-factor authentication with a time-based one-time password
When FIPS is enabled in Windows, our software uses Windows built-in cryptography, validated by NIST to FIPS 140-2 under certificates #2937, #2606, #2357, and #1892. On Windows XP and 2003, our software uses the Crypto++ 5.3.0 FIPS DLL, originally validated by NIST under certificate #819 (historical). When FIPS mode is not enabled, additional non-FIPS algorithms are supported.
Current Bitvise software versions (8.36 and higher) use the following cryptographic implementations for different algorithms, on different versions of Windows:
Algorithm | Windows XP, Server 2003 | Windows Vista to 8.1, Server 2008 to 2012 R2 | Windows 10, Server 2016 to 2019 |
|---|---|---|---|
| Signature | |||
| RSA | Crypto++ 5.3 | Windows CNG | Windows CNG |
| Ed25519 | n/a | DJB | DJB |
| ECDSA (NIST curves) | Crypto++ 5.3 | Windows CNG | Windows CNG |
| ECDSA/secp256k1 | Crypto++ 5.3 | OpenSSL | Windows CNG |
| 1024-bit DSA | Crypto++ 5.3 | Windows CNG | Windows CNG |
| Non-standard DSA | Crypto++ 5.3 | Crypto++ 5.6 | Crypto++ 5.6 |
| Key exchange | |||
| Classic DH | Crypto++ 5.3 | Windows CNG | Windows CNG |
| Curve25519 | n/a | DJB | DJB |
| ECDH (NIST curves) | Crypto++ 5.3 | Windows CNG | Windows CNG |
| ECDH/secp256k1 | Crypto++ 5.3 | OpenSSL | Windows CNG |
| Encryption | |||
| AES | Crypto++ 5.3 | Windows CNG | Windows CNG |
| 3DES | Crypto++ 5.3 | Windows CNG | Windows CNG |
| Integrity | |||
| GCM | n/a | Windows CNG | Windows CNG |
| HMAC-SHA2 | Crypto++ 5.3 | Windows CNG | Windows CNG |
| HMAC-SHA1 | Crypto++ 5.3 | Windows CNG | Windows CNG |
This product includes software developed by the OpenSSL Project for use in the OpenSSL Toolkit. (http://www.openssl.org/)
This product includes cryptographic software written by Eric Young (eay@cryptsoft.com).
Before you begin
Using SSH public key authentication to connect to a remote system is a robust, more secure alternative to logging in with an account password or passphrase. SSH public key authentication relies on asymmetric cryptographic algorithms that generate a pair of separate keys (a key pair), one 'private' and the other 'public'. You keep the private key a secret and store it on the computer you use to connect to the remote system. Conceivably, you can share the public key with anyone without compromising the private key; you store it on the remote system in a .ssh/authorized_keys directory.
To use SSH public key authentication:
- The remote system must have a version of SSH installed. The information in this document assumes the remote system uses OpenSSH. If the remote system is using a different version of SSH (for example, Tectia SSH), the process outlined below may not be correct.
- The computer you use to connect to the remote server must have a version of SSH installed. This document includes instructions for generating a key pair with command-line SSH on a Linux or macOS computer, and with PuTTY on a Windows computer.
- You need to be able to transfer your public key to the remote system. Therefore, you must either be able to log into the remote system with an established account username and password/passphrase, or have an administrator on the remote system add the public key to the
~/.ssh/authorized_keysfile in your account. - Two-factor authentication using Two-Step Login (Duo) is required for access to the login nodes on IU research supercomputers, and for SCP and SFTP file transfers to those systems. SSH public key authentication remains an option for researchers who submit the 'SSH public key authentication to HPS systems' agreement (log into HPC everywhere using your IU username and passphrase), in which you agree to set a passphrase on your private key when you generate your key pair. If you have questions about how two-factor authentication may impact your workflows, contact the UITS Research Applications and Deep Learning team. For help, see Get started with Two-Step Login (Duo) at IU and Help for Two-Step Login (Duo).
Set up public key authentication using SSH on a Linux or macOS computer
To set up public key authentication using SSH on a Linux or macOS computer:
- Log into the computer you'll use to access the remote host, and then use command-line SSH to generate a key pair using the RSA algorithm.
To generate RSA keys, on the command line, enter:
- You will be prompted to supply a filename (for saving the key pair) and a password (for protecting your private key):
- Filename: To accept the default filename (and location) for your key pair, press
EnterorReturnwithout entering a filename.Alternatively, you can enter a filename (for example,
my_ssh_key) at the prompt, and then pressEnterorReturn. However, many remote hosts are configured to accept private keys with the default filename and path (~/.ssh/id_rsafor RSA keys) by default. Consequently, to authenticate with a private key that has a different filename, or one that is not stored in the default location, you must explicitly invoke it either on the SSH command line or in an SSH client configuration file (~/.ssh/config); see below for instructions. - Password: Enter a password that contains at least five characters, and then press
EnterorReturn. If you pressEnterorReturnwithout entering a password, your private key will be generated without password-protection.If you don't password-protect your private key, anyone with access to your computer conceivably can SSH (without being prompted for a password) to your account on any remote system that has the corresponding public key.
Your private key will be generated using the default filename (for example,
id_rsa) or the filename you specified (for example,my_ssh_key), and stored on your computer in a.sshdirectory off your home directory (for example,~/.ssh/id_rsaor~/.ssh/my_ssh_key).The corresponding public key will be generated using the same filename (but with a
.pubextension added) and stored in the same location (for example,~/.ssh/id_rsa.pubor~/.ssh/my_ssh_key.pub). - Filename: To accept the default filename (and location) for your key pair, press
- Use SFTP or SCP to copy the public key file (for example,
~/.ssh/id_rsa.pub) to your account on the remote system (for example,darvader@deathstar.empire.gov); for example, using command-line SCP:You'll be prompted for your account password. Your public key will be copied to your home directory (and saved with the same filename) on the remote system.
- Log into the remote system using your account username and password.If the remote system is not configured to support password-based authentication, you will need to ask system administrators to add your public key to the
~/.ssh/authorized_keysfile in your account (if your account doesn't have~/.ssh/authorized_keysfile, system administrators can create one for you). Once your public key is added to your~/.ssh/authorized_keysfile on the remote system, the setup process is complete, and you should now be able to SSH to your account from the computer that has your private key. - If your account on the remote system doesn't already contain a
~/.ssh/authorized_keysfile, create one; on the command line, enter the following commands:If your account on the remote system already has a~/.ssh/authorized_keysfile, executing these commands will not damage the existing directory or file. - On the remote system, add the contents of your public key file (for example,
~/id_rsa.pub) to a new line in your~/.ssh/authorized_keysfile; on the command line, enter:Download game stronghold crusader 2. You may want to check the contents of
~/.ssh/authorized_keysto make sure your public key was added properly; on the command line, enter: - You may now safely delete the public key file (for example,
~/id_rsa.pub) from your account on the remote system; on the command line, enter:Alternatively, if you prefer to keep a copy of your public key on the remote system, move it to your
.sshdirectory; on the command line, enter: - Optionally, repeat steps 3-7 to add your public key to other remote systems that you want to access from the computer that has your private key using SSH public key authentication.
- You now should be able to SSH to your account on the remote system (for example,
username@host2.somewhere.edu) from the computer (for example,host1) that has your private key (for example,~/.ssh/id_rsa):- If your private key is password-protected, the remote system will prompt you for the password or passphrase (your private key password/passphrase is not transmitted to the remote system):
- If your private key is not password-protected, the remote system will place you on the command line in your home directory without prompting you for a password or passphrase:
If the private key you're using does not have the default name, or is not stored in the default path (not
~/.ssh/id_rsa), you must explicitly invoke it in one of two ways: Make your own cakeanne 28 online, free games.- On the SSH command line: Add the
-iflag and the path to your private key.For example, to invoke the private key
host2_key, stored in the~/.ssh/old_keysdirectory, when connecting to your account on a remote host (for example,username@host2.somewhere.edu), enter: - In an SSH client configuration file: SSH gets configuration data from the following sources (in this order):
- From command-line options
- From the user's client configuration file (
~/.ssh/config), if it exists - From the system-wide client configuration file (
/etc/ssh/ssh_config)
The SSH client configuration file is a text file containing keywords and arguments. To specify which private key should be used for connections to a particular remote host, use a text editor to create a
~/.ssh/configthat includes theHostandIdentityFilekeywords.For example, for connections to
host2.somewhere.edu, to make SSH automatically invoke the private keyhost2_key, stored in the~/.ssh/old_keysdirectory, create a~/.ssh/configfile with these lines included:Once you save the file, SSH will use the specified private key for future connections to that host.
You can add multiple
HostandIdentityFiledirectives to specify a different private key for each host listed; for example:Alternatively, you can use a single asterisk (
*) to provide global defaults for all hosts (specify one private key for several hosts); for example:For more about the SSH client configuration file, see the OpenSSH SSH client configuration file on the web or from the command line (
man ssh_config).
Set up public key authentication using PuTTY on a Windows 10 or Windows 8.x computer
The PuTTY command-line SSH client, the PuTTYgen key generation utility, the Pageant SSH authentication agent, and the PuTTY SCP and SFTP utilities are packaged together in a Windows installer available under The MIT License for free download from the PuTTY development team.
After installing PuTTY:
- Launch PuTTYgen.
- In the 'PuTTY Key Generator' window, under 'Parameters':
- For 'Type of key to generate', select RSA. (In older versions of PuTTYgen, select SSH2-RSA.)
- For 'Number of bits in a generated key', leave the default value (
2048).
- Under 'Actions', click Generate.
- When prompted, use your mouse (or trackpad) to move your cursor around the blank area under 'Key'; this generates randomness that PuTTYgen uses to generate your key pair.
- When your key pair is generated, PuTTYgen displays the public key in the area under 'Key'. In the 'Key passphrase' and 'Confirm passphrase' text boxes, enter a passphrase to passphrase-protect your private key.If you don't passphrase-protect your private key, anyone with access to your computer will be able to SSH (without being prompted for a passphrase) to your account on any remote system that has the corresponding public key.
- Save your public key:
- Under 'Actions', next to 'Save the generated key', click Save public key.
- Give the file a name (for example,
putty_key), select a location on your computer to store it, and then click Save.
- Save your private key:
- Under 'Actions', next to 'Save the generated key', click Save private key.If you didn't passphrase-protect your private key, the utility will ask whether you're sure you want to save it without a passphrase. Click Yes to proceed or No to go back and create a passphrase for your private key.
- Keep 'Save as type' set to PuTTY Private Key Files (*.ppk), give the file a name (for example,
putty_private_key), select a location on your computer to store it, and then click Save. - If you wish to connect to a remote desktop system such as Research Desktop (RED), click Conversions > Export OpenSSH key, give the file a name (for example,
putty_rsa), select a location on your computer to store it, and then click Save.
- Under 'Actions', next to 'Save the generated key', click Save private key.
- Log into the remote system using your account username and password.
If the remote system does not support password-based authentication, you will need to ask system administrators to add your public key to the
~/.ssh/authorized_keysfile in your account (if your account doesn't have~/.ssh/authorized_keysfile, system administrators can create one for you). Once your public key is added to your account's~/.ssh/authorized_keysfile on the remote system.. - If your account on the remote system doesn't already contain a
~/.ssh/authorized_keysfile, create one; on the command line, enter the following commands:If your account on the remote system already has
~/.ssh/authorized_keys, executing these commands will not damage the existing directory or file. - On your computer, in the PuTTYgen utility, copy the contents of the public key (displayed in the area under 'Key') onto your Clipboard. Then, on the remote system, use your favorite text editor to paste it onto a new line in your
~/.ssh/authorized_keysfile, and then save and close the file. - On your computer, open the Pageant SSH authentication agent. This utility runs in the background, so when it opens, you should see its icon displayed in the Windows notification area.
- In the Windows notification area, right-click on the Pageant icon, select Add Key, navigate to the location where you saved your private key (for example,
putty_private_key.ppk), select the file, and then click Open. - If your private key is passphrase-protected, Pageant will prompt you to enter the passphrase; enter the passphrase for your private key, and then click OK.
If your private key is not passphrase-protected, Pageant will add your private key without prompting you for a passphrase.
Either way, Pageant stores the unencrypted private key in memory for use by PuTTY when you initiate an SSH session to the remote system that has your public key.
- On your computer, open the PuTTY SSH client:
- On the Session screen:
- Under 'Host Name (or IP address)', enter your username coupled with the hostname of the remote server that has your public key; for example:
- Under 'Connection type', make sure SSH is selected.
- In the 'Category' list on the left, navigate to the Auth screen (Connection > SSH > Auth). On the Auth screen, under 'Authentication methods', select Attempt authentication using Pageant.
- Return to the Session screen, and under 'Saved Sessions', enter a name (for example,
Deathstar), and then click Save. - Click Open to connect to your account on the remote system. With Pageant running in the background, PuTTY will retrieve the unencrypted private key automatically from Pageant and use it to authenticate. Because Pageant has your private key's passphrase saved (if applicable), the remote system will place you on the command line in your account without prompting you for the passphrase.
Technically, at this point, the setup is complete. In the future, whenever you log into your Windows desktop, you can run Pageant, add the private key, and then use PuTTY to SSH to any remote resource that has your public key. Alternatively, you can create a shortcut in your WindowsStartupfolder to launch Pageant and load your private key automatically whenever you log into your desktop. For instructions, finish the rest of the following steps. - On the Session screen:
- Open your
Startupfolder. PressWin-r, and in the 'Open' field, typeshell:startup, and then pressEnter. - Right-click inside the
Startupfolder, and then select New and Shortcut. - In the 'Type the location of the item' text box, enter the path to the Pageant executable (
pageant.exe) followed by the path to your private key file (for example,putty_private_key.ppk); enclose both paths in double quotes; for example: - Click Next, and then, in the 'Type a name for this shortcut' text box, enter a name for the shortcut (for example,
PAGEANT). - Click Finish.
Ssh Key For Sftp
The next time you log into your Windows desktop, Pageant will start automatically, load your private key, and (if applicable) prompt you for the passphrase.
